Conversation
cfe7560 to
120a4b7
Compare
120a4b7 to
5f710be
Compare
🤖 Augment PR SummarySummary: This PR adds SRP (Secure Remote Password) authentication support for AFP, matching the SRP-6a/SHA-1 behavior used by Apple Time Capsule/macOS. Changes:
Technical Notes: SRP verifier file format is 🤖 Was this summary useful? React with 👍 or 👎 |
5f710be to
f6920bb
Compare
f6920bb to
4d13f7c
Compare
|
false alarm, it works when you use the correct password 😅 |
4d13f7c to
c051bce
Compare
c051bce to
fb19d0b
Compare
fb19d0b to
d17ed27
Compare
d17ed27 to
b4e4073
Compare
|
Tested and working here. |
|
Very cool! Well done indeed.. I'll do a proper code review in the next couple of days |
Implement the SRP (Secure Remote Password) UAM for AFP, as used by Apple Time Capsule. The protocol uses SRP-6a with SHA-1, MGF1 KDF, and RFC 5054 group #2 (1536-bit). afppasswd is modified to operate on SRP storage file by default, which stores per-user salts and verifiers, while retaining the legacy RandNum functionality activated with the -r flag. An additional breaking change is that afppasswd -a now takes username as argument rather than previous positional username arugment. The containers now use SRP for authentication by default.
b4e4073 to
0849baa
Compare
|
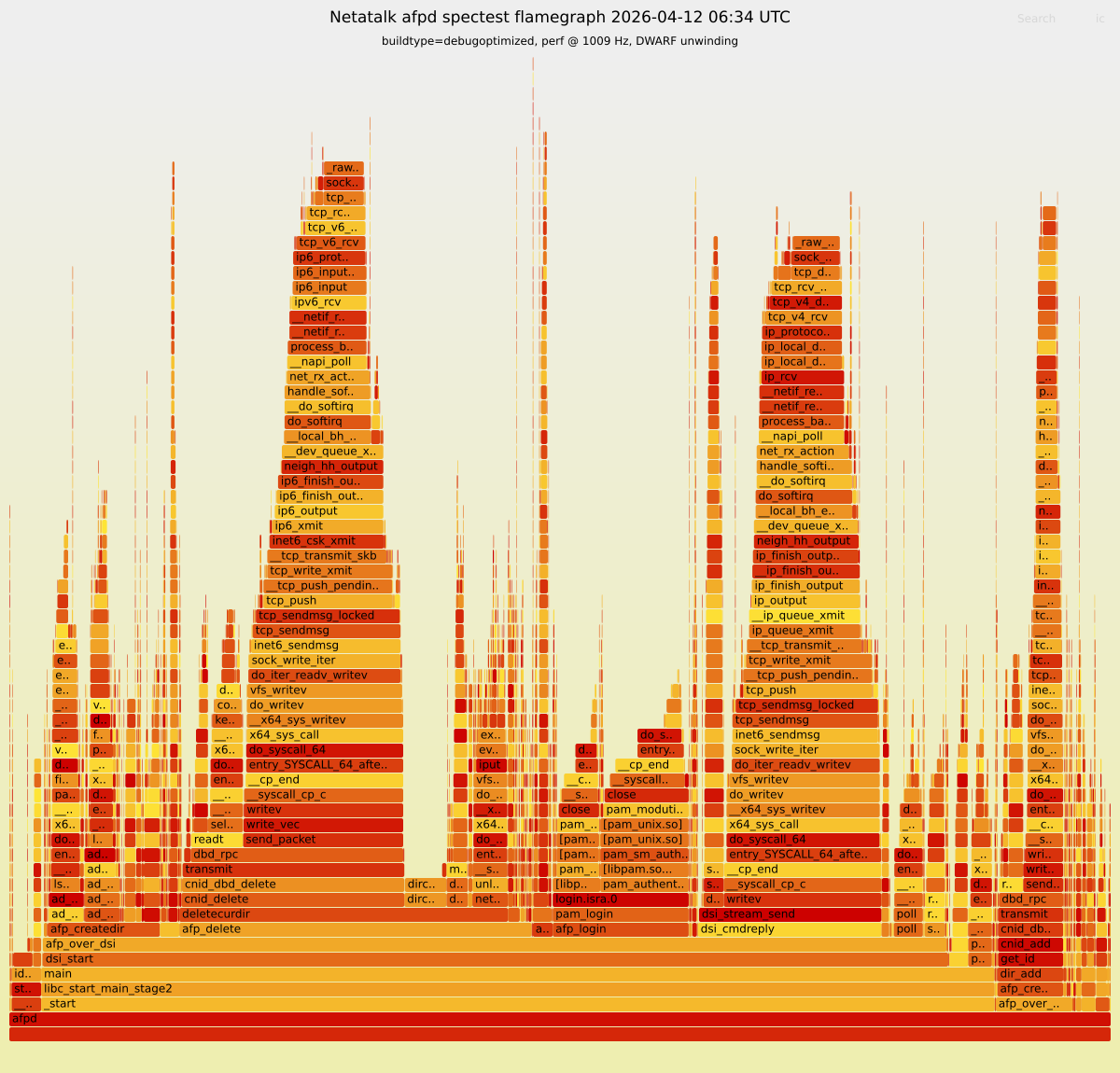
🔥 Spectest (AFP 3.4) - Flamegraph (AFP_ASSERT active)Commit: 🔥 Open interactive Flamegraph (SVG) 🔝 Top 10 leaf functions
|
|
QR review shows this is a high quality PR 🙂 This looks to be a well-engineered implementation of the SRP-6a protocol. Minor comments; LGTM - Impressive work! 🚀 |
|
@andylemin thanks for the review!
I have been going back and forth about this; Do you have any advice here, whether to emulate Time Capsule fully or attempt to adhere to the AFP spec where appropriate? |
I think we have seen enough examples of Apple not complying with the AFP spec themselves, so I think we should go with what is required for Time Capsule and just acknowledge any spec violations? |



Implement the SRP (Secure Remote Password) UAM for AFP, as used by Apple Time Capsule.
The protocol uses SRP-6a with SHA-1, MGF1 KDF, and RFC 5054 group #2 (1536-bit).
afppasswd is modified to operate on SRP storage file by default, which stores per-user salts and verifiers, while retaining the legacy RandNum functionality activated with the -r flag.
An additional breaking change is that afppasswd -a now takes username as argument rather than previous positional username arugment.
The containers now use SRP for authentication by default.