-
Notifications
You must be signed in to change notification settings - Fork 0
security issue #1
Description
Hello,
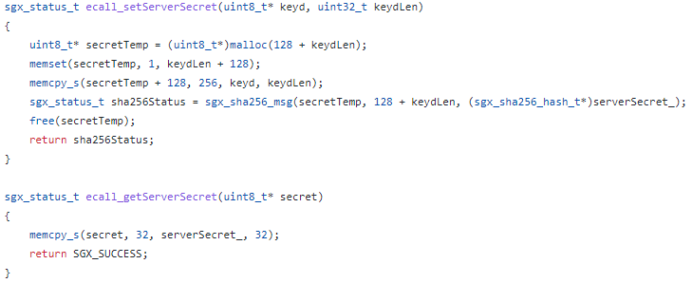
we‘ve found some arbitrary write problems in both km_enclave and pow_enclave.The following functions in km_enclave lead to such problems.
A malicious adversary can provide any address inside or outside enclave as secret([user-check]) to take control of write address, while continuously change keyd’s value until the first byte of serverSecret_ become expected value. Then the attacker can write the expected byte wherever he want. Getting an expected byte takes 2^8 tries. By doing one byte each time, the time complexity is O(n*2^8) for N bytes control. That’s not a large burden to change a return address or else.
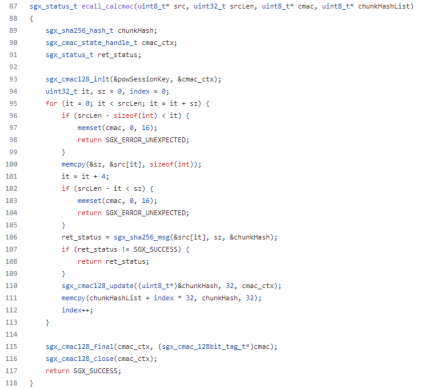
In pow_enclave, the situation is similar.
Attacker can use chunkHashList instead of secret and src instead of keyd, and the chunkHash takes place of serverSecret.
Thanks.
yudhui